The AI-driven solution for more effective vulnerability management
ThreatFinder automatically assesses and prioritizes vulnerabilities based on their risk, allowing the most critical threats to be addressed first.


Why Doesn’t Traditional Vulnerability Management Work Anymore?
The number and complexity of vulnerabilities are constantly increasing. This makes the classic approach—manual analysis of vulnerabilities by staff—more challenging. ThreatFinder automates and optimizes this process by prioritizing threats and providing all relevant information on vulnerabilities. This allows your team to focus on what truly matters. Start with ThreatFinder today to improve the quality and efficiency of your vulnerability management!
Advantages of ThreatFinder
-
![databased prioritized]()
Data-driven prioritization of your vulnerabilities
-
![process optimization]()
Process optimization through standardized procedures
-
![effective info]()
All information at a glance
-
![emplyee productivity]()
Increase in employee productivity
-
![sustainable documentation]()
Sustainable documentation of vulnerability management
-
![clear overview]()
Clear overview of your threat landscape
Insights of our Community
FAQs
-
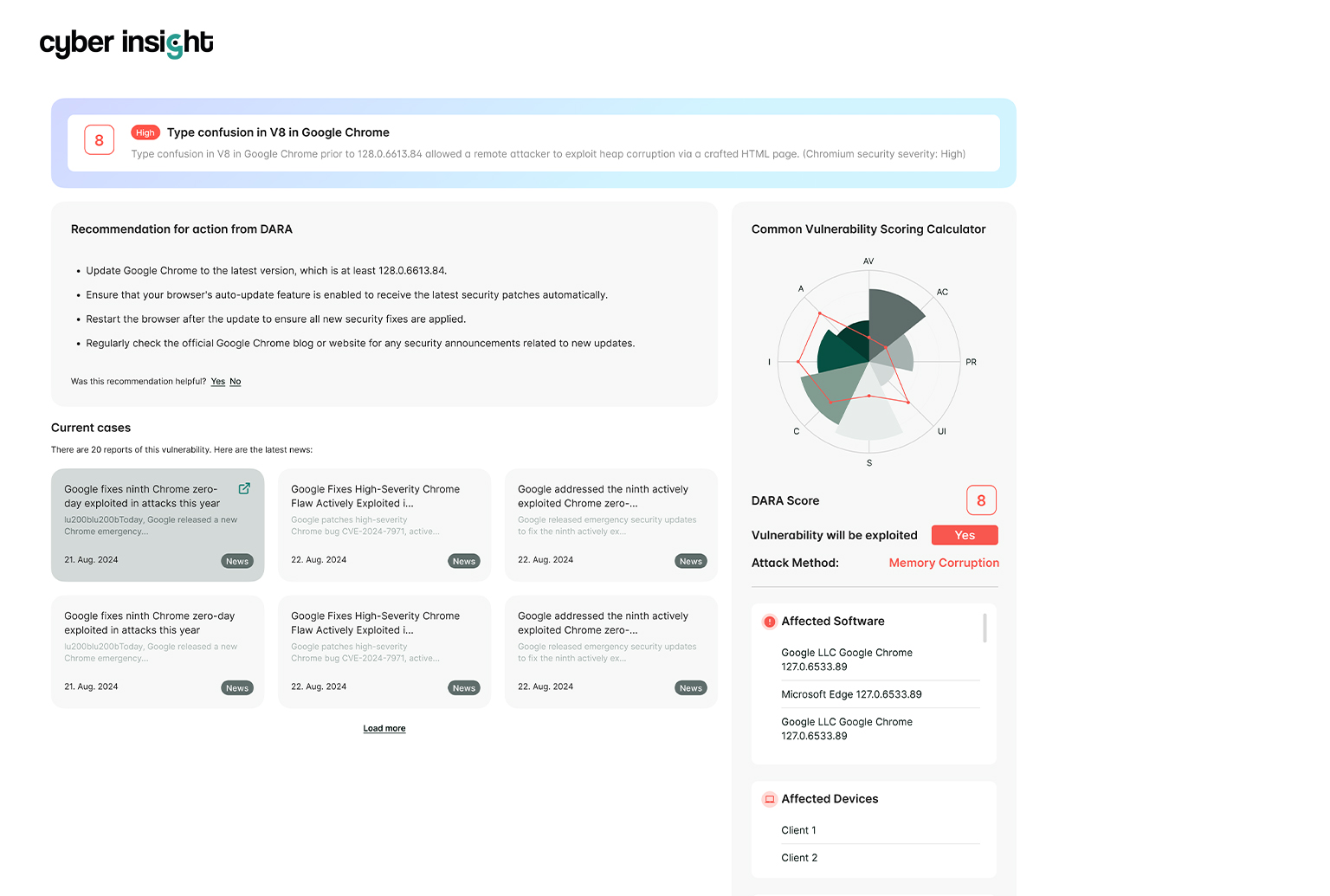
ThreatFinder is an AI-based threat intelligence solution that prioritizes and assesses vulnerabilities and provides clear insights into their exploitation.
-
We specialize in enterprises and therefore cannot provide security-related analysis for private IT infrastructures.
-
ThreatFinder consolidates all relevant information, concrete actions, and current news about vulnerabilities in one place. This reduces the need for security analysts, leading to higher efficiency and lower costs in vulnerability management.
-
The entire Cyber Insight platform is hosted in Europe in compliance with data protection regulations.
-
The Cyber Insight Exploit Prediction (CIEX) model by DARA outperforms the Exploit Prediction Scoring System (EPSS) used by many cybersecurity companies, including industry leaders like AWS, Cisco, and WIZ, by a factor of 4. Our proprietary technology makes vulnerability predictions actionable.
-
Current cyber trends, news, exploits and customer-specific vulnerabilities are analyzed and evaluated.
-
To achieve a high level of security, it is necessary to use third-party products, such as a firewall.